Utilizing Encryption to Strengthen PostgreSQL Database Security
Organizations deal with different types of data including very crucial information that needs to be stored in a database.Security is a key aspect of consideration for ensuring sensitive data such as...
View ArticleWhat is the COINiD Cold Storage Solution?
Cryptocurrency users all over the world are always looking for ways to keep their funds safe and secure. That is a pretty big challenge, especially when buying a hardware wallet is not an option....
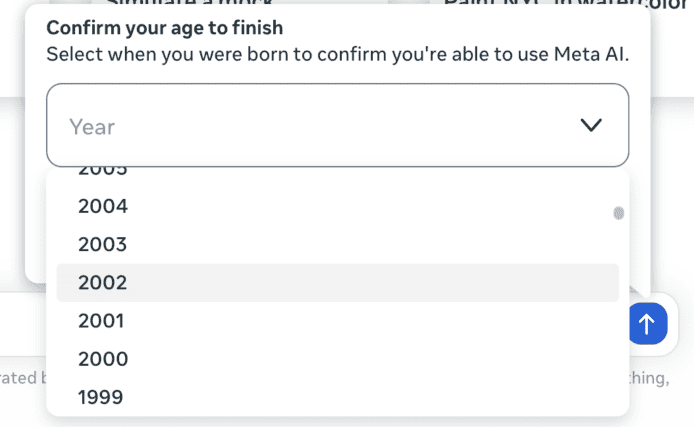
View ArticleBeta Client Now Supports Secure Password Reset.
We are happy to let you know that we have updated our new beta client and added a secure password reset feature. This feature enables you to reset your Tutanota login credentials in case you lose your...
View ArticleApplication-Layer DDoS Attack Protection with HAProxy
HAProxy’s high-performance security capabilities are utilized as a key line of defense by many of the world’s top enterprises. Application-layer DDoS attacks are aimed at overwhelming an application...
View ArticleGAO Report: Expired Certificate Allowed Extended Exfiltration
GAO Report: Expired Certificate Allowed Extended Exfiltration kdobieski Fri, 11/09/2018 08:33 I was not entirely surprised by the revelation of the role the expired certificateplayed.Nearly two years...
View ArticleAndroid Security Auditing (Investigating Unauthorized Screenshots)
About six months ago, I discovered something on my smartphone that horrified me: I went to undelete a file in DiskDigger , and I stumbled upon a plethora of unexpected jpegs: screenshots of my...
View ArticleKoadic: Security Defense in the Age of LoL Malware, Part IV
One of the advantages of examining the gears inside Koadic is that you gain low-level knowledge into how real-world attacks are accomplished. Pen testing tools allow you to explore how hackers move...
View ArticleGift Guide: The best security and privacy tech to keep your friends safe
Libertarian on lockdown? Privacy minded or paranoid? Security is more front of mind today than ever befroe. If it’s not a company vacuuming up your data or nation states trying to hack your email, it’s...
View ArticleEmail Stealing Emotet Banking Trojan Resurrected in New Extensive Spam Campaign
A new ample spam campaign is spreading the Emotet banking Trojan to unsuspecting victims via maliciously crafted emails as discovered by ESET Research in November. Emotet, infamous for being a modular...
View ArticleHackers Target Bitcoins and USCYBERCOM Shares Malware | Avast
Cryptocurrency code breached, targeting Bitcoin exchanges Earlier this week, hackers successfully breached StatCounter, a leading web analytics platform, in an attempt to steal bitcoins from...
View ArticleVoronoi diagram with ggvoronoi package with Train Station data
I’ve always been curious to make Voronoi diagram, I just think they are beautiful! When I came across data set with train stations in Japan. I instantly thought this would be great data sets to make...
View Article汉庭桔子宜必思…超5亿条开房信息泄露后,企业这样做才能保护用户
(点击图片进入小程序) 大数据时代,您的个人信息还安全吗? 近几年,信息泄露的 安全事件多次发生,您是否也在担心? 企业能够为用户做些什么呢,专家解答在后半部分,我们先看几个案例: 2018年8月14日,华住旗下汉庭、桔子、宜必思等数十家品牌酒店,140G共约5亿条客户信息在暗网出售,内容包括姓名、手机、身份证号、开房记录、账号密码、家庭地址等详细数据;...
View Article我的挑书手段
双十一,一年一度的”屯书日“又到了。 鄙人生平无其它购物嗜好,唯有购书。 在电子书横行的时代,各类读书应用都在崛起,比如”微信读书“、”QQ阅读“、”掌阅“等,个人习惯用微信读书,因为有社交好友的阅读推荐,以及公司送的读书券,所以基本也都是免费的,这个才是重点。...
View Article业绩不断增长,什么“救”了埃森哲?
前段时间,埃森哲公布了最新财务报告。财报显示,第四季度的净收入超过100亿美元,以美元和当地货币计均同比增长11%。稀释每股收益为1.58美元,同比增长7%。主营业务利润率达14.3%,同比增长10个基点。新订单额达108亿美元。...
View ArticleGartner六大安全趋势 | 数据安全是关乎企业生死存亡的核心要素
前言 近日,Gartner研究团队副总裁Peter Firstbrook在美国佛罗里达州举办的顶级安全趋势大会上表示,数据安全是关乎企业生死存亡的核心要素之一。 最近几年里,各大公司发生的数据泄漏事件造成的影响和结果不可谓不惨烈,严守数据安全是企业的底线,此外云端系统安全、机器学习、AI和日益增长的网络威胁也是Gartner认为在2019年要着重关注的安全发展趋势。...
View Article高防服务器如何挑选?
高防服务器主要是针对DDos、CC流量攻击而出现的。由于当前互联网中存在很多黑客攻击,最为普遍就是DDos攻击,对目标网络或者服务器进行资源占取,导致服务器出现拒绝式服务。租用高防服务器,可以通过防火墙,数据监测、牵引系统等对流量性攻击进行有效削弱,从而起到防御作用。那么,高防服务器如此有用,又应当如何挑选呢?...
View Article每天抵抗4000万次黑客访问,这个天猫双11,阿里巴巴如何守卫消费者权益?
摘要: 安全小二从来不缺惊心动魄。 文/天下网商记者 宁函夏 很多时候战役开始之前其实胜负已定。 阿里安全的工程师们也早就开始了布局――这一年里他们无数次打退网络世界里的攻击,也曾碰到过黑灰产团伙在警察面前为避罪而生吞U盘,协助警方把窝在大山里的诈骗分子一锅端掉,早已是家常便饭。 天猫双11就在眼前,现在,他们守在屏幕前,枕戈待旦,像个守门员一般,坚守着阿里巴巴的安全生命线。...
View Article高防云服务器可以防御哪些类型的攻击?
高防云服务器是一款可防御大规模DDoS攻击、CC攻击的云服务器类型,能够帮助网站应对拒绝服务攻击,对恶意流量进行有效鉴别和清洗,为单个客户提供网络安全维护。那么,高防云服务器具体可以防御哪些类型的攻击呢 1、带宽消耗攻击...
View ArticleConcerns Rise Over Backdoored Smart Contracts
Ever since the Slockit DAO hack, some if not most ethereum smart contracts have used a fail safe mechanism that is actually very vulnerable and not very fail safe. Ethereum is Turing complete. So you...
View ArticleThe Gamification Of Fitbit: How an API Provided the Next Level of tRaining
(This article was first published on Stories by Matt.0 on Medium , and kindly contributed toR-bloggers) “Anyone can look for fashion in a boutique or history in a museum. The creative explorer looks...
View Article