I spent about 2 hours on the following scenario and located the root cause was lacking a static route on Palo Alto, so I decided to summarize every step here for further reference. Here is the topology:

EVE-NG Topology The left part is the office, and the right part is Internet 10.0.56.5 of R6 was NATed to IP: 10.0.17.3 by Palo Alto which establishes IPSec tunnel with R8: 10.0.78.8 Traffic from 5.5.5.0/24 to 8.8.8.0/24 will be forward over the #1 IPSec All device in ‘LAN’ could access ‘Internet’ via Port Translation
Procedure:
1. Initial Palo Alto
Console access Palo Alto with username/password: admin/admin, and configure MGMT IP 172.16.185.132 (I have bridged the mgmt interface of Palo Alto to my laptop). Here are the commands for the initialization:
configure edit deviceconfig system set ip-address 172.16.185.132 netmask 255.255.255.0 commitNote: Remember to execute ‘commit’ on CLI or Web GUI after the modification.
2. Navigate https://172.16.185.132 in the browser, login with the username/password: admin/admin

Palo Alto-Dashboard
3. Configure Interface Profiles: Permit ping traffic from both LAN and Internet to Palo Alto interfaces for connectivities testing

Palo Alto-Interface management profile
4. Configure interface: ethernet1/1

Palo Alto-Interface configuration-Zone-1

Palo Alto-Interface configuration-Zone 2

Palo Alto-Interface configuration-IP Address-1

Palo Alto-Interface configuration-IP Address-2

Palo Alto-Interface configuration-Management Profile
5. Configure interface: ethernet1/2, almost same steps to ethernet1/1 but with different IP and Zone IP: 10.0.17.1/24, Zone: Internet.
6. Configured IPs, routing protocol on R5, R6, R7, R8 then run connectivity testing.
R5: Ethernet0/0 10.0.56.5/24, Ethernet0/1 10.0.15.5/24, Loopback0: 5.5.5.5/24, Default route with gateway: 10.0.15.1
R6: Ethernet0/0 10.0.56.6/24, Default route with gateway: 10.0.56.5
R7: Ethernet0/0 10.0.78.7/24, Ethernet0/2 10.0.17.7/24
R8: Ethernet0/0 10.0.78.8/24, Loopback0 8.8.8.8/24, Static route to 10.0.17.0/24 with next hop: 10.0.78.7
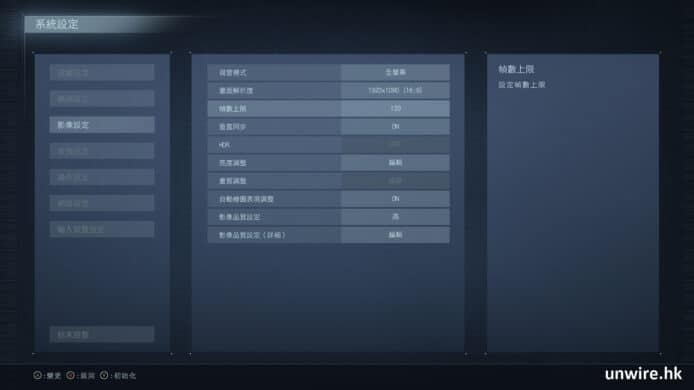
7. Configure routing on Palo Alto
Default route with next hop: 10.0.17.7
Static route to 10.0.56.0/24 with next hop 10.0.15.5

Palo Alto-Route
8. Configure PAT for Requirement #4: traffic from LAN to Internet

Palo Alto-PAT-1

Palo Alto-PAT-2

Palo Alto-PAT-3
9. Creating Service group before the Security policy for IPSec traffic: UDP 500 and UDP 4500

Palo Alto-Service

Palo Alto-Service Group
10. Configure NAT for requirement #3 IPSec

Palo Alto-NAT-1 : Servie-IPSec
Note: The destination Address is the IP of Peer IP, the IP is: 10.0.78.8/32 in my case.
Optional: Set Service to ‘Any’ for all applications

Palo Alto-NAT-Optional: Service Any

Palo Alto-NAT-3

Palo Alto-NAT/PAT-Overall view of Step 9 and Step 10
11. Since LAN and Internet are two different zones, security policies are required for the traffic. From LAN to Internet:

Palo Alto-Security Policy-1

Palo Alto-Security Policy-2

Palo Alto-Security Policy-3

Palo Alto-Security Policy-4
12. Security policy for IPSec

Palo Alto-Security Policy
13. Verify connectivities on all routers
Note: Security policy for Ping traffic in two different Zones, Ping will fail if only the application: ICMP was permitted, the service: ‘Ping’ is also required.
14. Configure IPSec on R6 and R8. Check all routers configuration from here .
15. On R5, execute ‘ping 8.8.8.8 source 5.5.5.5’
LAN-R5#ping 8.8.8.8 source 5.5.5.5 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 8.8.8.8, timeout is 2 seconds: Packet sent with a source address of 5.5.5.5 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 2/3/7 ms LAN-R5# LAN-R6#show crypto isakmp sa IPv4 Crypto ISAKMP SA dst src state conn-id status 10.0.78.8 10.0.56.6 QM_IDLE 1001 ACTIVE IPv6 Crypto ISAKMP SAInternet-R8#show crypto isakmp sa IPv4 Crypto ISAKMP SA dst src state conn-id status 10.0.78.8 10.0.17.3 QM_IDLE 1001 ACTIVE IPv6 Crypto ISAKMP SA